Investigation Report on the World of Warcraft Cheat "Sopabox-cn"
Report Publication Notice:
The initial version of this investigative report was completed on May 15, 2025. Following completion, due to the need for prudent coordination with Blizzard Entertainment, NetEase Games, and related partner units, and to ensure the successful apprehension of the criminal organization, we decided to postpone public disclosure.
As the primary core suspects have been placed under mandatory measures in accordance with the law, and this disclosure will not negatively impact further investigation or the integrity of the evidence chain, we now officially release this report.
【Legal Risk Notice and Reading Declaration】
This article is based on publicly available information (such as website historical snapshots, business registration information, etc.) and intelligence provided by multiple anonymous sources to organize and analyze the software "Sopabox-cn" and related controversial events. All individuals and entities mentioned in this article should be presumed innocent until convicted by final effective judgment from judicial authorities. Therefore, this article uniformly uses neutral terms such as "suspected," "alleged," and "purported" for description, and designations (such as "suspected core operator") are for investigative lead guidance only and do not represent any final judgment by the author on the nature of conduct or legal status.
Legal provisions analysis, profit scale estimations, and other content in this article are theoretical discussions and model deductions based on public information and do not constitute any form of legal opinion, financial audit conclusion, or factual accusation, nor are they final determinations of involved amounts. All information is subject to official announcements from game manufacturers and final investigations and judgments by judicial authorities.
Abstract
This report aims to conduct a comprehensive, in-depth investigation and analysis of the "Sopabox-cn" cheat program that sparked major controversy within the World of Warcraft community and its suspected related cybercrime activities. The report begins with a malicious incident involving player "Player D" (game ID "Nobita") using cheats and subsequently doxxing and physically threatening those who exposed him. Using this as an entry point, the report details the process of reactivating investigation into the "Sopabox-cn" cheat and establishes a clear key action timeline, documenting critical nodes such as submitting technical samples to game manufacturers and communicating with multiple parties.
Table of Contents
- 1. Introduction
- 2. Investigation Reactivation and Key Timeline
- 3. Origin and Operating Model
- 4. Source of Leads and Analysis
- 5. Case Insights and Enforcement
- 6. Black Market Scale Estimation
- 7. Legal Discussion
- 8. Future Evolution Predictions
- 9. User Profile Analysis
- 10. Technical Appendix: Cheat Classification
- 11. Other Discovered Cheats
- 12. Related Links
- 13. Appendix: Evidence Screenshots
1. Introduction
1.1 Background and Origin of Investigation
Hello everyone, I am Hasan.
After going AFK in version 9.1.5 (and deactivating all social media accounts), I thought I had completely disconnected from all disputes surrounding China's World of Warcraft servers.
Until ⏰ 2025.05.13 - 11:24, a message from an old friend recounting "gossip" that filled me with righteous indignation.
Here's what happened: A player with ID "Nobita" ("Player D") used a cheat called "Sopabox-cn" to push WCL rankings. After being discovered and exposed by internet users, "Player D" became furious, not only doxxing the whistleblower but threatening they must apologize, declaring he would "chop off their hands."
Even more outrageous was "Player D's" guild master—that "great, glorious, and correct" individual who once vowed to "keep the honor on China servers" only to have that honor revoked—"Player D's Guild Master". Rather than dealing with "Player D", he openly protected him, declaring: "We have someone with a bad temper in our raid (referring to 'Player D'), you've hit a brick wall."
Only after I had my concerns seriously conveyed to "Player D's Guild Master" through disillusionment did his tone shift 180 degrees, claiming: "He ('Player D') is no longer in our raid."
Additionally, regarding certain unverified information circulating online, I have submitted it as leads to relevant authorities for handling as required. After confirming this preliminary incident received attention, my focus shifted to analyzing the program itself—"Sopabox-cn."
1.2 Legal Risk Analysis of Involved Parties' Conduct
⚠️ Legal Knowledge Education Only
This section is solely for popularizing general legal knowledge, aiming to explain potential legal red lines that related conduct may touch, and does not constitute legal characterization of any specific individual or incident. Final determination requires judicial authorities to rule according to law.
For example, behaviors such as "doxxing" (human flesh search) and verbal threats that appeared in this incident may, legally speaking, violate the following provisions:
- Article 253-1 of the Criminal Law of the People's Republic of China [Crime of Infringing on Citizens' Personal Information]. This provision stipulates that violating relevant state regulations by selling or providing others' personal information to third parties, where circumstances are serious, shall be punished with fixed-term imprisonment of not more than three years or criminal detention, and/or a fine; where circumstances are especially serious, with fixed-term imprisonment of not less than three years but not more than seven years, and a fine.
- Article 293 of the Criminal Law of the People's Republic of China [Crime of Picking Quarrels and Provoking Trouble]. This explicitly stipulates that "chasing, intercepting, insulting, or threatening others, where circumstances are vile" and "causing disturbances in public places, creating serious disorder in public places" can constitute this crime. Cyberspace is not beyond the law and is equally applicable.
Note: Even if involved parties are located overseas (such as Japan), this will create certain difficulties for domestic police enforcement. However, it is not without legal basis: according to the Criminal Law's principles of territorial jurisdiction and protective jurisdiction, as long as the result of criminal conduct occurs within Chinese territory (i.e., victims suffered harm within China), Chinese judicial authorities have jurisdiction.
2. Investigation Reactivation and Key Action Timeline
2.1 Background of Investigation Reactivation
As early as ⏰ 2024.01.12 - 22:18, hunter player "Chen Jun" had already reported the "Sopabox-cn" cheat to me. Although I initiated preliminary investigation at the time, my interest was lackluster, feeling that pure PVE tools had limited impact. Nevertheless, I maintained continued attention to this program through specific channels.
At that time, I also reverse-engineered the "Sopabox-cn" client, but its code quality was so atrocious—the kind that would explode if you looked at it one more time—that I couldn't be bothered to delve deeper and set it aside.
However, given the egregious nature of this incident (Nobita threatening to chop off hands), I officially reactivated investigation at ⏰ 2025.05.14 - 15:11. As someone with late-stage OCD, I ultimately traced this cheat's origins thoroughly.
Moreover, at ⏰ 2025.05.14 - 22:24, I had delivered the "Sopabox-cn" client code sample and technical report obtained through reverse analysis to Blizzard via an industry contact at Microsoft.
2.2 Key Action Timeline
Here is the key timeline for this operation:
⏰ 2025.05.14 - 15:11 Investigation Reactivation:
After confirming proper handling of the "hand-chopping" incident preliminarily, I officially reactivated comprehensive investigation into the "Sopabox-cn" cheat.
⏰ 2025.05.14 - 22:24 Client Code Sample Submission:
I delivered the client code sample and technical report obtained through reverse analysis to Blizzard via a friend at Microsoft.
⏰ 2025.05.15 - 08:24 Blizzard Response:
Blizzard informed me they had begun taking ban action based on the client code sample. Meanwhile, I was absorbed in creating Hearthstone cards of China server players using AI.
⏰ 2025.05.20 - 16:20 Community Discussion Obstructed:
I attempted to post related analysis on the NGA forum, but posts were repeatedly deleted, specific reasons unknown.
⏰ 2025.05.29 - 20:20 NetEase Involvement:
Staff from NetEase's relevant team contacted me.
⏰ 2025.05.30 - 13:18 Multi-party Coordination:
I packaged all gathered intelligence into a brief along with "Sopabox-cn" client samples, submitting them separately to NetEase teams and cybersecurity law enforcement departments.
⏰ 2025.06.03 - 21:52 Official Announcement:
China World of Warcraft Operations Team released 《Severe Crackdown on All Cheats! World of Warcraft Violation User Penalty Announcement》, naming "Sopabox-cn" and confirming its cheat nature.
⏰ 2025.06.05 - 14:22 Suspect Activity:
According to sources, after the official announcement, online activity indicators of "Suspected Core Operator A" suggest they may no longer be in mainland China.
⏰ 2025.06.06 - 12:27 Follow-up:
NetEase staff informed me they would initiate internal investigation into this matter.
⏰ 2025.06.17 - 12:12 Information Exchange and Support:
NetEase officially conducted first offline communication with relevant departments regarding investigation of the "Sopabox-cn" cheat, exchanging information and providing evidence support.
⏰ 2025.06.19 - 11:12 Cheat Update and New Form Emergence:
"Sopabox-cn" received version update and shifted to distribution via private file transfer. The new client was discovered to have added WeChat scanning and local disk scanning functionality, which was immediately relayed to friends in WeChat's related security department.
⏰ 2025.07.21 - 13:32 Evidence Preservation and Technical Identification:
NetEase officials, together with relevant witnesses, went to public security departments for offline statements and submitted the new "Sopabox-cn" client for professional technical identification.
⏰ 2025.07.28 - 11:47 Identification Complete and Assessment Phase:
Technical identification report issued, evidence chain organization and comprehensive case assessment work officially initiated.
⏰ 2025.07.31 Deployment and Apprehension Preparation:
Apprehension operation against this criminal ring officially entered deployment and arrangement phase.
⏰ 2025.08.08 Target Locking and Concentrated Apprehension:
Relevant authorities launched concentrated apprehension operation against core members, successfully controlling its primary suspects.
⏰ 2025.08.15 Key Technical Personnel Apprehended:
Relevant authorities further investigated and apprehended members who provided technical support and developed cheats, further consolidating the evidence chain.
⏰ 2025.09.04 Key Suspect Captured:
Relevant authorities successfully apprehended another key member, individual codenamed "B", preserving related evidence.
⏰ 2025.09.08 Lead Emergence and Voluntary Surrender:
As apprehension operations continued and police pressure mounted, some insider personnel who provided leads to the ring and some who participated as rotation authors began recognizing the risks and successively voluntarily surrendered, confessing some criminal facts.
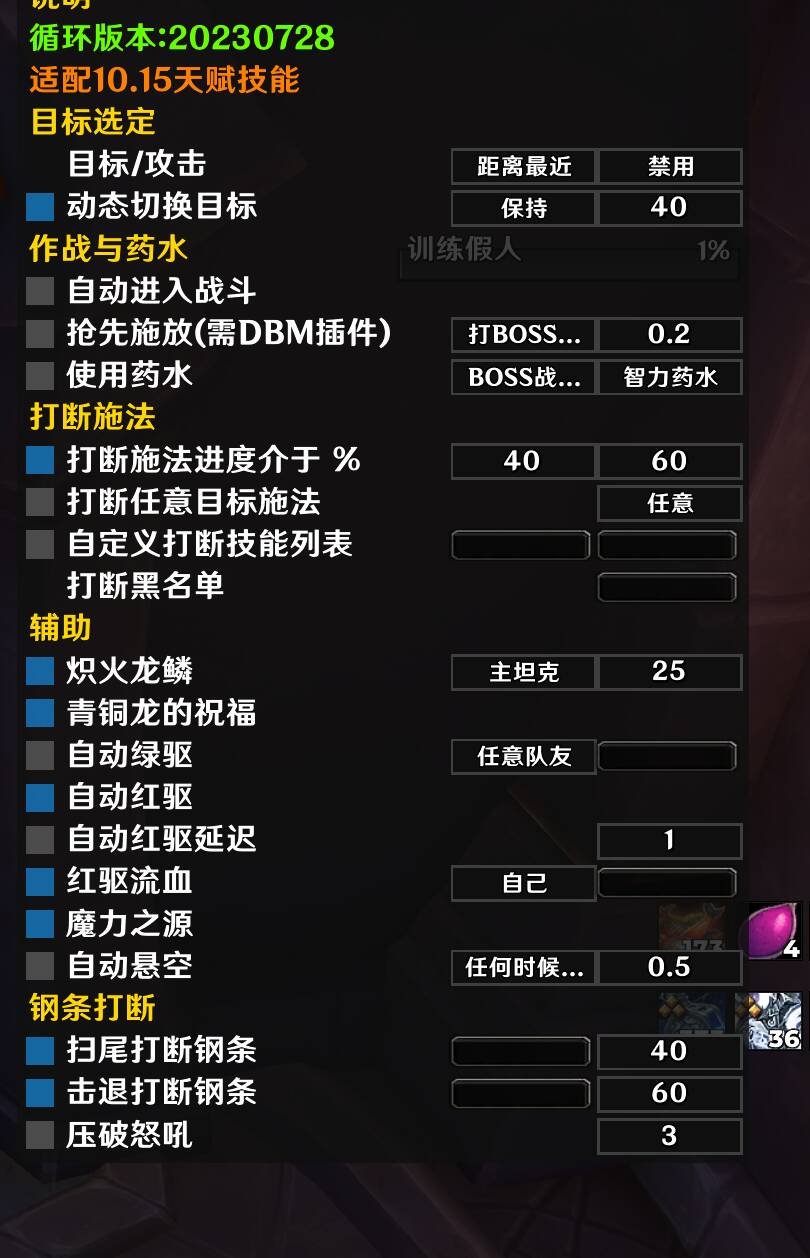
3. Origin and Operating Model of the "Sopabox-cn" Cheat
3.1 Historical Evolution
This cheat software originated from Soapbox Rotations, initially created by a German developer residing in Switzerland during the Mists of Pandaria (MOP) expansion (contemporaneous with HonorBuddy).
In July 2016, during the Legion expansion, "Suspected Core Operator A" collaborated with a programmer to reverse-engineer the original software, launching the "Cracked World of Warcraft Soapbox Chinese Version."
To avoid risk, the software was renamed "Sopabox-cn" during patch 9.0, and in August 2024 renamed again to "Sopabox-cn/GES" to obfuscate and return to China servers.
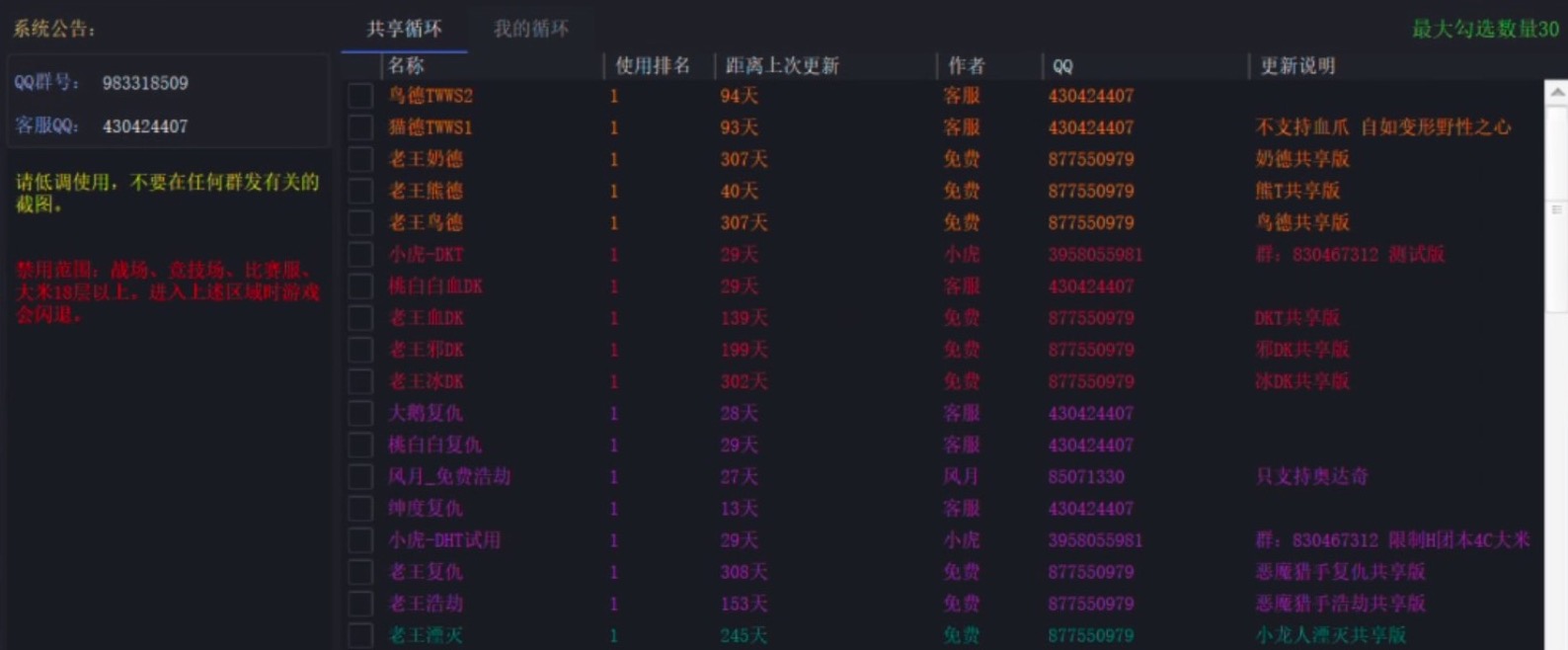
The cheat includes multiple class-specific script packages, written by different authors and paid for through private WeChat or Alipay accounts.
3.2 Pricing and Profit Model
According to "Sopabox-cn's" original official website information:
- 2016-2024 Period: Price was "150 RMB/month hardware-locked, 200 RMB/month not hardware-locked"
- After China Server Return (2024+):
- 4800 RMB/year to purchase the cheat unlocker core
- Plus 400 RMB/month to purchase usage rights
- Currently around 2000 users, peaking at 5000 users
Regarding custom rotations for various classes, users purchase directly from rotation authors individually, typically 200 RMB/month.
3.3 Sales Channels
Regarding sales channels, "Sopabox-cn" initially sold through Taobao stores, later shifting to card merchant platforms for transactions. These transactions allegedly may involve money-running and other illegal activities.
3.3.1 Root Cause of Long-term Concealment: Precise Exploitation of Regulatory Blind Spots
Before reviewing reasons for the ring's ultimate exposure, we must first answer a key question: How could such an organization with such glaring operational security holes operate safely for nearly a decade?
The answer lies in their precise exploitation of structural "blind spots" in each regulatory domain between game operators (NetEase) and law enforcement (police), thereby constructing a dual-safety survival space.
1. For Game Operators: Information Chasm and Inefficient Reporting Mechanisms
The cheat's distribution model constituted the first line of defense. Rather than advertising through public channels, it relied on highly closed social networks like QQ groups, WeChat groups, and power-leveling circles for "friend introduction"-style viral spread.
This model naturally excluded penetration by external regulatory forces, forming a high-trust internal circle. Cheating users as beneficiaries would never voluntarily expose themselves; ordinary players who perceived cheat existence mostly provided subjective descriptions lacking technical evidence like "his damage is abnormal" or "operation too perfect."
This severe information asymmetry resulted in NetEase security teams facing massive low-quality, difficult-to-verify reports, like finding a needle in a haystack, greatly consuming their regulatory resources and effectiveness.
2. For Law Enforcement: Professional Barriers and Case Filing Thresholds
The observation that "most cybercops don't play WoW" precisely identified the core obstacle faced at enforcement level—cross-domain professional knowledge barriers.
For law enforcement personnel to understand technical concepts like "DLL injection," "memory reading," "unlocking native functions" and effectively connect them with behavioral evidence like "WCL ranking anomaly data" within the game world requires crossing knowledge chasms across gaming, programming, and law dimensions.
In summary, the ring operated precisely in the regulatory gap between "operators lacking evidence, unable to reach" and "enforcers facing high professional barriers, difficult filing." The former due to technical and information limitations could not eradicate its survival soil; the latter due to barriers and resource constraints could not launch thunderous strikes—these two factors jointly created its years-long "lawless zone."
4. Source of Leads and Analysis Process
4.1 Process of Identifying Primary Leads
【Solemn Statement】
All analysis processes below are based on publicly available online information (such as website historical snapshots, enterprise business information) and intelligence provided by anonymous sources. All mentioned personnel are only "analysis subjects" based on leads; whether they constitute violations or crimes ultimately requires legal determination by judicial authorities. This article aims to organize leads and does not constitute factual accusation against anyone.
-
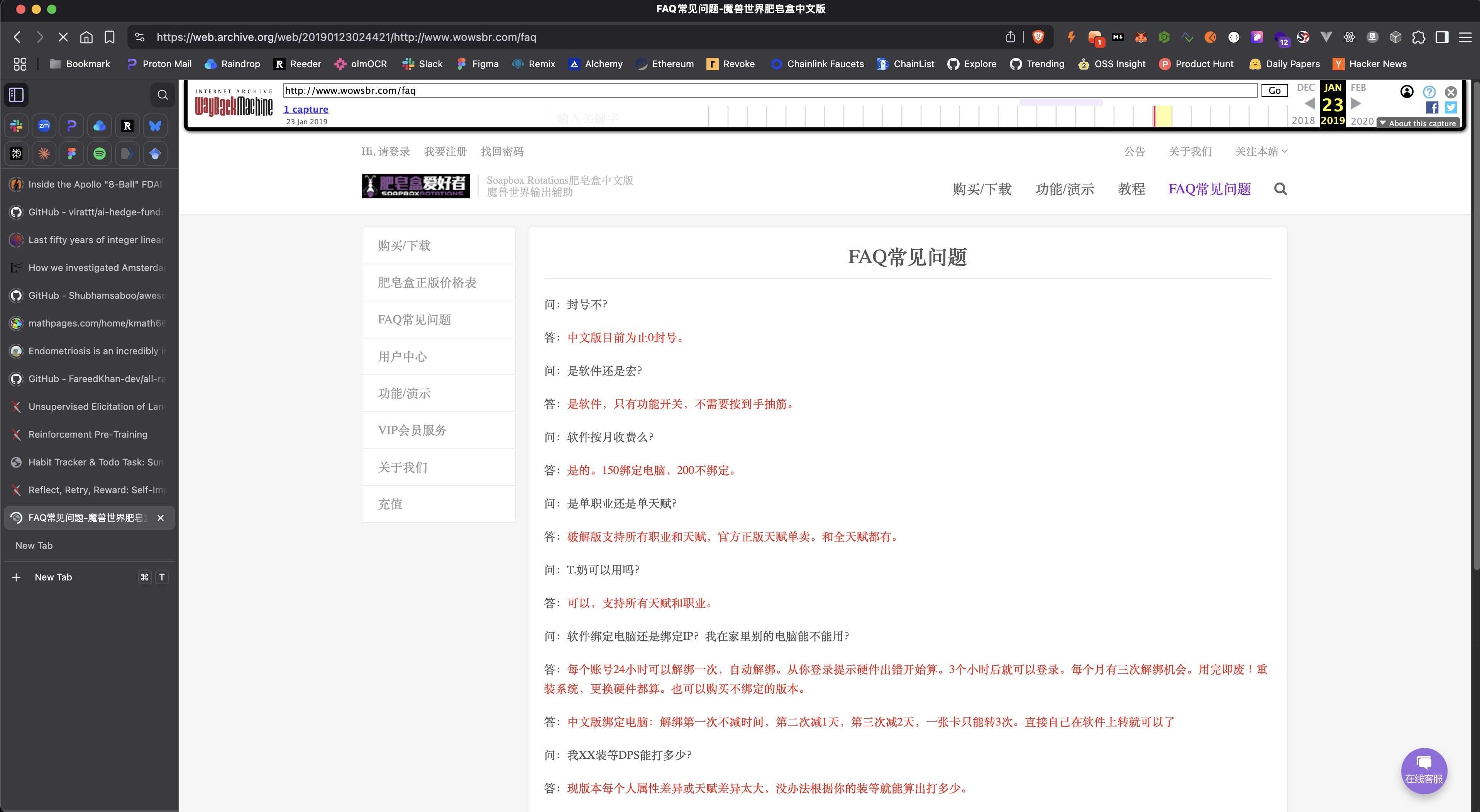
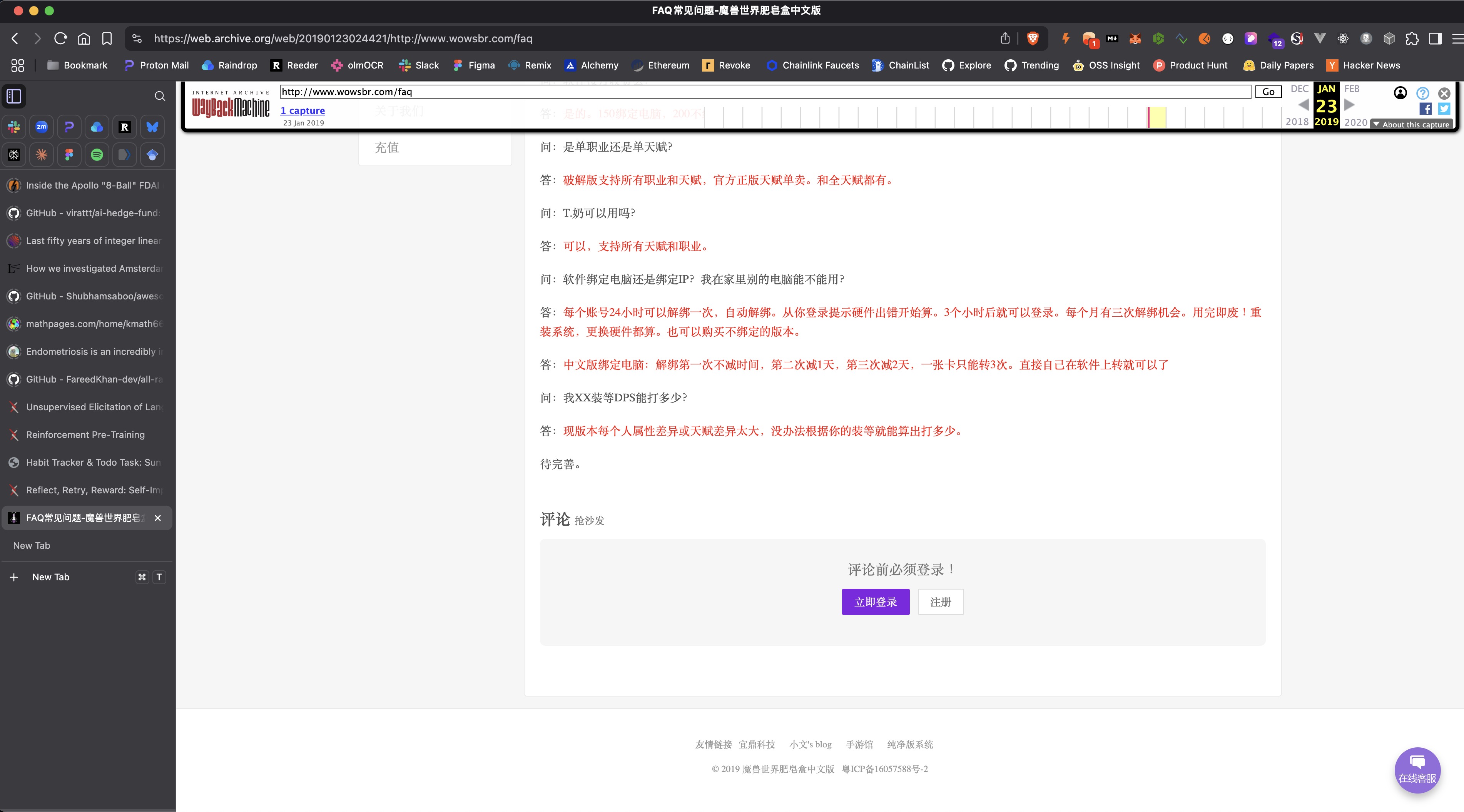
⏰ 2025.05.16 - 09:11 Through Wayback Machine querying
http://www.wowsbr.com/historical mirrors, website registration number Yue ICP Bei 16057588-2, upon inquiry matched Taobao store real name discovered, identifying one "Suspected Core Operator A". -
⏰ 2025.05.16 - 09:20 Through Wayback Machine querying
http://www.wowsbr.com/historical mirrors, discovered page footer contained a friend link including Dingtian Technology Co., Ltd. Through public business information inquiry, discovered a company partner highly matching multiple characteristics of "Suspected Core Operator A", while we discovered another partner suspected to be "Second-Generation Developer", warranting further attention. -
⏰ 2025.05.16 - 09:30 Through Wayback Machine querying
http://www.wowsbr.com/historical mirrors, discovered traces related to Taobao sales channels, with "Chinese Version Soapbox" period Taobao sales store link: https://shop69527830.world.taobao.com/ -
⏰ 2025.05.16 - 09:31 Through Wayback Machine querying
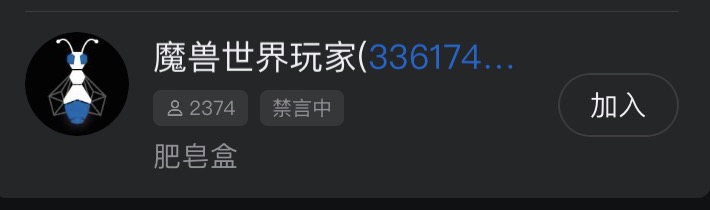
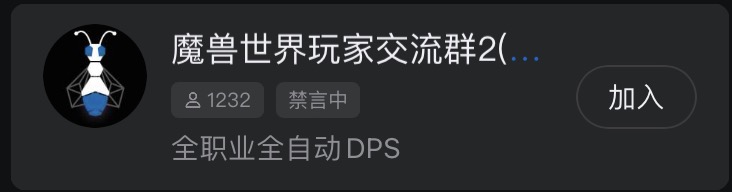
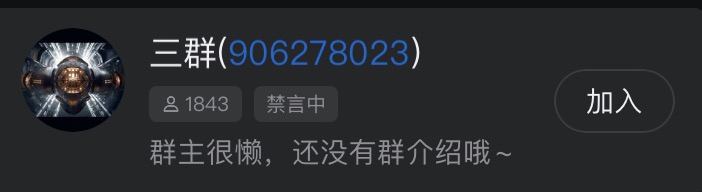
http://www.wowsbr.com/historical mirrors, learned their sales channels were mainly QQ groups, mirrors showed groups 1 and 2, NetEase official-provided report information contained group 3. Through total member count of three sales QQ groups, we estimated total user count at approximately 5450. After cross-verification with another independent source's user information, results highly matched. This information can serve as key important lead for this operating ring's cheat sales. -
⏰ 2025.05.16 - 09:40 Through Wayback Machine querying
http://www.wowsbr.com/historical mirrors, discovered payment addresses changed after they stopped using Taobao channels, links:http://9527faka.com/andhttps://www.cs3000.xyz - ⏰ 2025.05.16 - 09:55 Through payment verification, Taobao store https://shop69527830.world.taobao.com/ was registered under "Suspected Core Operator A's" real name, meaning investigating this store's transaction flow could serve as investigation of "Suspected Core Operator A's" connection to this software sales key important lead.
-
⏰ 2025.05.16 - 10:12 Through https://web.archive.org querying
http://www.wowsbr.com/historical mirrors, learned that between 2016-2024, this cheat's selling price was "150 RMB/month hardware-locked, 200 RMB/month not hardware-locked." Cross-verified information with internal sources, confirming information accuracy. This information can estimate this operating ring's illegal proceeds between 2016-2024. - ⏰ 2024.08.20 - 08:32 Through internal sources and earlier reports received by NetEase official cross-verification, confirmed authenticity of "Sopabox-cn's" price adjustment after China server return in 2024 to "400 RMB/month or 4800 RMB/year". This information can estimate this operating ring's illegal proceeds from 2024 to present.
- ⏰ 2025.05.20 - 22:32 According to core source's allegation, one "Suspected Core Member B" in the ring may have used their personal real-name account for payments. Meaning investigating "Suspected Core Member B's" private WeChat and Alipay transaction flows could potentially constitute investigation of related fund flows as key important lead.
-
⏰ 2024.02.24 - 22:32 According to information provided by core source, the cheat team's servers have user game character IDs they can query. This information has 2 points of value:
- Can provide information to Blizzard for banning
- Can use game character information and user information in this operating ring's backend to strike against power-leveling services and streamers
- Applicable to Criminal Law of the People's Republic of China Article 285 regarding crime of illegally obtaining computer information system data and illegally controlling computer information systems. Application point: illegally obtaining computer information (this cheat's memory reading satisfies this), and investigating whether some streamers and game power-levelers used cheats for commercial profit provided possibility.
- According to industry observation, some game power-levelers' monthly income is considerable; streamers' income may be even higher. Once this information is obtained by judicial authorities, it could serve as evidence determining some users used cheats for illegal profit. For potential tax evasion, tax authorities also have corresponding audit jurisdiction.
- Using striking cheats and striking studios as propaganda showing NetEase's excellence as agent
-
⏰ 2025.06.04 - 22:12 Due to China World of Warcraft Operations Team's release Severe Crackdown on All Cheats! "World of Warcraft" Violation User Penalty Announcement naming "Sopabox-cn", this may have become one factor prompting "Suspected Core Operator A" to change location.
- This suspect allegedly left mainland China then blocked China servers, began operating Taiwan and US/EU "Sopabox-cn" cheats.
- ⏰ 2025.06.05 - 23:32 According to informant-provided information, "Involved Person C" contacted "Suspected Core Operator A" to purchase "Sopabox-cn" source code but was refused, attempted cracking underlying code themselves. Involved person source also alleged another "Involved Person C", besides allegedly selling rotation packages under the "Sopabox-cn" platform, may also be involved in organizing rotation writing tutorials and creating/selling auxiliary programs for other games (like PUBG), possibly even related to private server activities. All above information provided unilaterally by sources, pending verification.
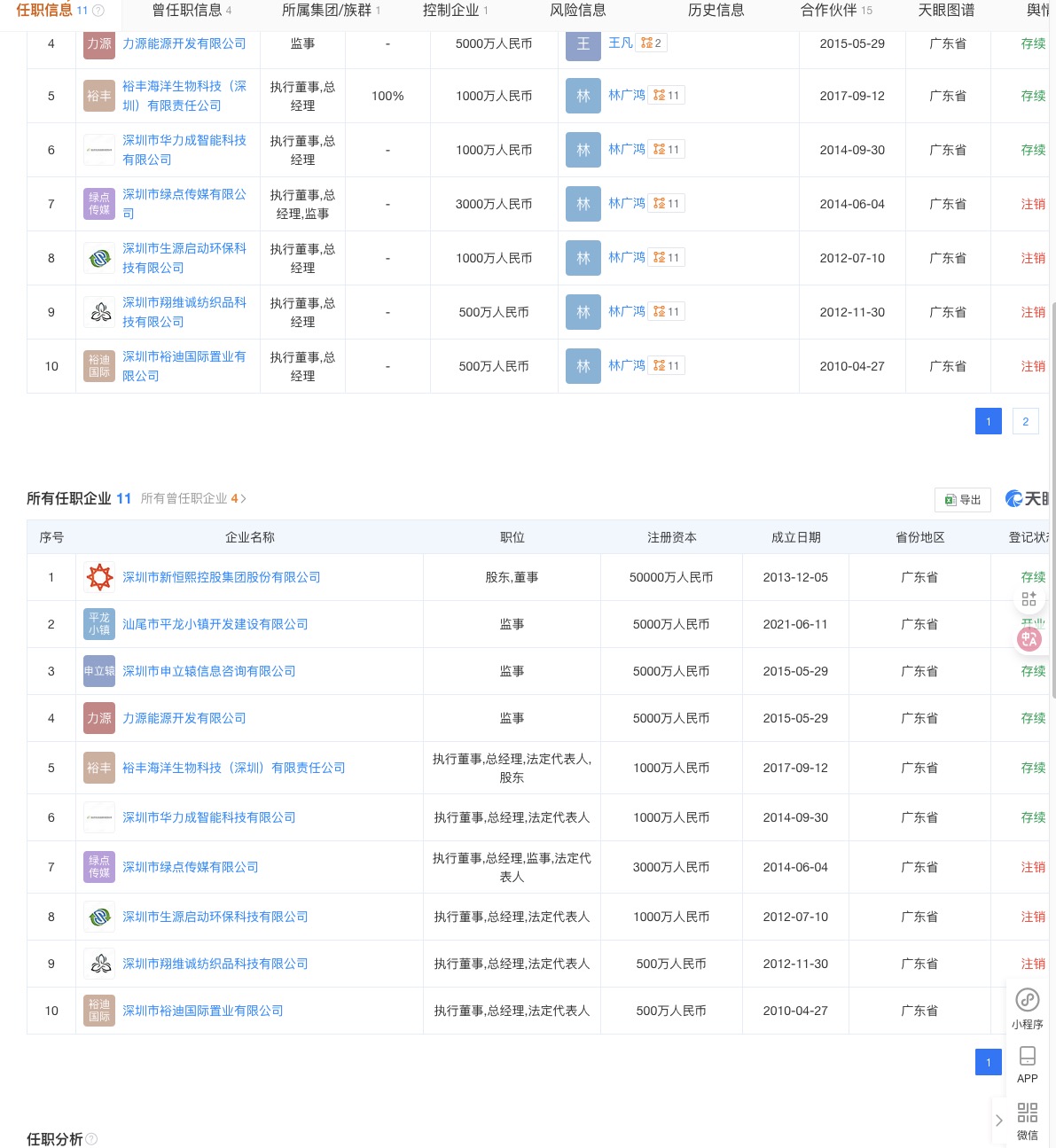
- ⏰ 2025.05.16 - 12:12 When querying cancelled Dingtian Technology Co., Ltd. information, I continued tracking other associated companies under "Suspected Core Operator A's" name. Through Tianyancha platform discovered "Suspected Core Operator A" is member of Shenzhen Xinghengxi Holding Group. Their company "Shenzhen Hualiecheng Intelligent Technology Co., Ltd." shows operational anomalies. Another company "Yufeng Marine Biotechnology (Shenzhen) Co., Ltd." (establishment time and registered capital requiring further cross-verification), its establishment time has suspected connection with certain key years of cheat income, providing possibility for further fund flow tracking.
- ⏰ 2025.05.16 - 14:22 Further investigation revealed "Suspected Core Operator A" also owns a company named "Shenzhen Painaomen Network Technology Co., Ltd.", a small-micro enterprise. Its registered business content allegedly used to legitimize cheat illegal income, providing channels for "laundering" funds.
4.2 Composition of "Sopabox-cn" Ring
- Sales
- "Suspected Core Operator A"
- "Suspected Core Member B"
- Developers
- 2016-2024 First-Generation Developer
- 2024-2025 Second-Generation Developer
- 2016-2025 Framework Maintenance Developer
- Rotation Authors
- Over 20 individuals
4.3 Major Sales Channels
- Initially used Taobao store sales
- Later adopted card merchant platforms
- Most cases used Alipay or WeChat real-name transfers; rotation authors' payments basically all Alipay or WeChat real-name transfers.
4.4 Post-mortem Analysis of Suspected Operating Team's Exposure
This ring appeared organizationally tight but actually had multiple fatal weaknesses making it vulnerable under professional investigation. Overall, this supposed operating ring of "Sopabox-cn" demonstrated lack of professionalism across multiple levels, exposing numerous weaknesses.
1. Extremely Weak Operational Security Awareness (Core Weakness):
- Real-Name Exposure: Primary "Suspected Core Operator A" used a registered website (
Yue ICP Bei 16057588-2) and real-name verified Taobao store for cheat sales during early operations. This was the most fatal mistake, directly tying virtual illegal activities to his real identity. - Personal Account Payments: "Suspected Core Member B" (whose professional background requires verification) and multiple "rotation authors" long used their own real-name WeChat and Alipay for payments. This provided clear, irrefutable fund flow evidence for police.
- Associated Information Leaks: Early website left a friend link pointing to their partner company (Dingtian Technology), further exposing "Suspected Core Operator A's" real-world social network.
2. Chaotic Internal Security and Personnel Management:
- Easily Penetrated: Reportedly, investigators had established effective information sources within the organization's development team and core user groups as early as 2024. This showed the ring lacked basic background checks and confidentiality mechanisms; internal intelligence could be easily obtained.
- Complex Member Backgrounds: The ring allegedly included former NetEase employees ("Suspected Core Member B"), which was not only a huge PR liability but gave NetEase stronger motivation to intervene and "clean house."
3. Uneven Technical Capabilities:
- Poor Code Quality: The cheat client's code was "excessively atrocious in quality," reducing reverse engineering difficulty, allowing me to relatively easily obtain its client code samples.
- Dependence on External Source Code: This cheat wasn't entirely original but developed through reverse-engineering early software
Soapbox Rotations, with unstable technical foundation.
4. Poor Member Psychological Quality, Reckless Behavior:
- User Arrogance Backfires: The incident's catalyst was user "Nobita" ("Player D's") doxxing and "hand-chopping" threats, plus guild master "Player D's Guild Master's" open protection. Such extreme behavior inevitably elevated what was originally a gaming circle controversy to criminal level, ultimately drawing my attention.
- Primary Suspected Operator Allegedly Left Country: "Suspected Core Operator A's" movements after official announcement suggested they had allegedly left the country. This showed lack of crisis response plans and psychological preparation; organizational structure fragile.
5. Case Insights and Extended Enforcement Recommendations
The downfall of the "Sopabox-cn" ring's significance shouldn't end with individual case conclusion but should be viewed as a precious sample for dissecting World of Warcraft and even the entire gaming industry's black market ecosystem. Through this case, we not only see an organization's operation and collapse but gain insight into the deeply entangled industry chains behind it.
Based on discoveries from this investigation, we propose the following two highly feasible extended enforcement recommendations aiming to achieve "surface" cleanup from "point" breakthrough, hoping to conduct systematic, root-level governance of China's World of Warcraft cheat black market.
5.1 Strategy One: Using "Rotation Authors" as a Hub to Implement Network-based Investigation and Dismantle the Technical Supply System
This case exposed over 20 "rotation authors", the most critical yet most easily overlooked "technical infrastructure" in the entire cheat industry. Their core characteristic is "mobile operations," like technical mercenaries whose service targets are definitely not limited to "Sopabox-cn" alone. They are core technical nodes maintaining normal operations of multiple cheat rings (whether retail or classic servers).
Therefore, we recommend law enforcement departments and NetEase security teams jointly establish a special task force, listing these "rotation authors" as high-priority investigation targets. Action path as follows:
- Fund Chain Tracing: Conduct deep penetration analysis of their known Alipay, WeChat and other real-name payment accounts, tracking all fund sources. Each "development fee" from different rings is a lead pointing to new targets.
- Social Network Penetration: Analyze their friend relationships and group chat records through QQ, WeChat and other social accounts. Behind these seemingly routine social behaviors hides the entire contact network of cheat developers and sellers.
- Technical Profiling: Analyze their code style, technical habits, even embed "digital watermarks" in code. When this code appears in other cheats, precise tracing can be achieved.
Through this "people-to-case" network investigation model, strikes can upgrade from single rings to cleanup of entire upstream technical supply networks. Each fully verified "rotation author's" complete service trajectory could lead to multiple hidden cheat rings, ultimately achieving strategic effect of "casting one big net, catching entire pond of fish."
5.2 Strategy Two: Targeting "Commercial Cheating" for Precise Strikes to Deter and Shrink the Demand Market
If "rotation authors" are the black market's supply side, then streamers and power-leveling studios using cheats for commercial profit are the demand side's "cancer cells." They are not only loyal cheat consumers but "live advertisements" for cheat effectiveness; their behavior greatly stimulates ordinary players' emulation psychology and consumption desire.
Their conduct has transcended "ordinary cheating" scope; income obtained through streaming tips, power-leveling orders, account trading fully meets the legal definition of "illegal proceeds," with sufficient conditions for pursuing legal responsibility.
Therefore, we recommend adopting a "set examples, point leads surface" strategy:
- Lock Top Targets: Select several streamers or studios with greatest influence and most lucrative gains among major streaming platforms or power-leveling communities as primary strike targets.
- Joint Platform Action: NetEase and public security departments can jointly work with major streaming platforms to ban and publicly announce them on grounds of "spreading and using illegal software for profit," cooperating with judicial procedures to confiscate illegal proceeds.
- Strengthen PR Publicity: Use cases of striking top users as typical examples for network-wide publicity, clearly conveying to all players: "In China, using cheats for profit is not just against rules but illegal, facing dual strikes of account bans and legal sanctions."
This can directly sever the "cheat-traffic-monetization" black profit chain, more deterrent than simply banning tens of thousands of ordinary accounts. Through precise strikes on demand market "opinion leaders," can effectively deter potential users, guide community atmosphere, fundamentally compress cheat survival space, achieving "removing fuel from under the cauldron" effect.
6. Theoretical Deduction and Estimation of Black Market Scale
【Solemn Legal Statement and Model Limitation Warning】
All following profit scale estimations are purely based on public information, some anonymous sources, and numerous assumptions to construct theoretical mathematical models, whose sole purpose is abstractly revealing potential commercial scale of such gray industry chains for industry research and warning purposes. This model contains numerous uncertainties and subjective assumptions, absolutely does not reflect nor represent any real financial data. Its calculation results do not constitute factual accusation of any individual or entity's illegal proceeds amounts, much less equal judicial authorities' determined "illegal proceeds" or "case amounts." Real case amounts must undergo strict judicial audit procedures for final determination. Any behavior directly equating this theoretical model deduction results with facts or using as accusation evidence is incorrect and contrary to the author's intention.
Because "Sopabox-cn" in NetEase era + Taiwan server era and after China server return were two products by the same ring but two different developers. Pricing also different, so calculated separately. Only estimating "Sopabox-cn" core illegal proceeds; due to different pricing for custom rotations for various classes, all individual payments, difficult to estimate, so not estimating custom rotation illegal proceeds.
6.1 Revenue Estimation During NetEase and Taiwan Server Period
Estimating "Sopabox-cn" revenue during NetEase era + Taiwan server era
Version Division and User Count Assumptions
1. Legion expansion (2016—2018)
- Operation time: 24 months
- Initial users: 5000 (hardware-locked users), ending users: 2500 (decline).
- Average locked user count: 5000 + 25002 = 3750
- Revenue:
- Hardware-locked users: 3750 users × 150 RMB × 24 months = 13,500,000 RMB
- Assume unlocked users: initial 1000, ending 600
- Average unlocked user count: 1000 + 6002 = 800
- Revenue:
- Non-hardware-locked users: 800 users × 200 RMB × 24 months = 3,840,000 RMB
- Total Revenue: 13,500,000 + 3,840,000 = 17,340,000 RMB
2. Battle for Azeroth expansion (2018—2020)
- Operation time: 24 months
- Initial users: 5000 (hardware-locked users), ending users: 3000 (decline).
- Average locked user count: 5000 + 30002 = 4000
- Revenue:
- Hardware-locked users: 4000 users × 150 RMB × 24 months = 18,000,000 RMB
- Assume unlocked users: initial 2000, ending 1200
- Average unlocked user count: 2000 + 12002 = 1600
- Revenue:
- Non-hardware-locked users: 1600 users × 200 RMB × 24 months = 7,680,000 RMB
- Total Revenue: 18,000,000 + 7,680,000 = 25,680,000 RMB
3. Shadowlands expansion (2020—2022)
- Operation time: 24 months
- Initial users: 5000 (hardware-locked users), ending users: 2000 (decline).
- Average locked user count: 5000 + 20002 = 3500
- Revenue:
- Hardware-locked users: 3500 users × 150 RMB × 24 months = 12,600,000 RMB
- Assume unlocked users: initial 3000, ending 1000
- Average unlocked user count: 3000 + 10002 = 2000
- Revenue:
- Non-hardware-locked users: 2000 users × 200 RMB × 24 months = 9,600,000 RMB
- Total Revenue: 12,600,000 + 9,600,000 = 22,200,000 RMB
4. Dragonflight expansion (2022—August 2024)
- Operation time: 24 months
- Initial users: 5000 (hardware-locked users), ending users: 1500 (decline).
- Average locked user count: 5000 + 15002 = 3250
- Revenue:
- Hardware-locked users: 3250 users × 150 RMB × 24 months = 11,700,000 RMB
- Assume unlocked users: initial 3500, ending 1000
- Average unlocked user count: 3500 + 10002 = 2250
- Revenue:
- Non-hardware-locked users: 2250 users × 200 RMB × 24 months = 10,800,000 RMB
- Total Revenue: 11,700,000 + 10,800,000 = 22,500,000 RMB
Total Revenue Calculation
Adding each portion's revenue:
- Legion expansion revenue: 17,340,000 RMB
- Battle for Azeroth expansion revenue: 25,680,000 RMB
- Shadowlands expansion revenue: 22,200,000 RMB
- Dragonflight expansion revenue: 22,500,000 RMB
6.2 Revenue Estimation After China Server Return
Early Post-China Server Return (August 1, 2024—August 27, 2024)
- Operation time: 26 days
- Assume user count: 2000 users
- Revenue calculation (calculated daily):
- Price: 400 RMB/month
- Monthly rent calculated daily as:
400 30 RMB/day
-
Revenue = 2000 × 40030 × 26 ≈ 2000 × 13.33 × 26 ≈ 693,333.33 RMB
"World of Warcraft: The War Within" Launch (August 27, 2024—May 31, 2025)
- Operation time: 9 months (approximately 270 days)
- Assume user count remained at 2000 during this period
- Revenue calculation:
Revenue = 2000 × 400 × 9 = 7,200,000 RMB
Total Revenue
Adding both portions' revenue:
Therefore, estimated "Sopabox-cn" total revenue after China server return (August 2024 to May 2025) period is approximately 7,893,333 RMB.
(All data in this section are theoretical models based on public information and assumptions, not representing actual case value)
7. Legal Discussion on Potential Charges Related to Conduct
7.1 Analysis of Primary Charges
1. Criminal Law of the People's Republic of China Article 285 Paragraph 3: Crime of Providing Programs or Tools for Intrusion into or Illegally Controlling Computer Information Systems.
- Interpretation: This is the most direct, most commonly used legal provision for striking cheat creation and sales. This cheat by modifying or interfering with normal operation of World of Warcraft client (a computer information system), achieved automated operations, fully meeting elements of "providing......programs or tools for illegally controlling computer information systems."
- Sentencing Standards:
- Base penalty: Fixed-term imprisonment of not more than three years or criminal detention, and/or a fine.
- Where circumstances are especially serious: Fixed-term imprisonment of not less than three years but not more than seven years, and a fine.
2. Criminal Law of the People's Republic of China Article 217: Crime of Copyright Infringement.
- Interpretation: This software through "reverse engineering" cracked original software and modified game client's original data, constituting unauthorized reproduction, distribution, and transmission through information networks of computer software without copyright holder (Blizzard/NetEase) permission.
- Sentencing Standards: "Where illegal proceeds amounts are huge or other especially serious circumstances exist," fixed-term imprisonment of not less than three years but not more than ten years, and a fine.
3. (Potentially Involved) Criminal Law of the People's Republic of China Article 225: Crime of Illegal Business Operations.
- Interpretation: If cheat's operating model is determined to constitute illegal publishing, distribution and other conduct seriously disrupting market order, may also constitute this crime. But when more direct charges (like Article 285) exist, this charge usually serves as backup or supplement.
7.2 Legal Applicability Analysis
⚠️ Academic Discussion Only
Following analysis is solely academic discussion based on Criminal Law and related judicial interpretations, not constituting legal conclusions or trial predictions for any specific case.
-
For suspected organizers and core personnel of this software, from pure legal theory perspective, if their related conduct is verified by judicial authorities, then legally they may be evaluated as crime organizers; they are organizers, core developers, and primary beneficiaries.
Their suspected conduct's scale according to public leads may touch determination standards for "especially serious circumstances." According to Criminal Law and related judicial interpretations, for especially serious circumstances, legally prescribed penalty range is "fixed-term imprisonment of not less than three years but not more than seven years" criminal punishment, plus fines and confiscation of illegal proceeds.
Considering copyright infringement crime concurrence, according to China's legal principle of "choosing heavier crime for punishment" or "combined punishment for multiple crimes," in judicial practice, final sentencing will be comprehensively decided by courts based on all verified facts and evidence. According to related provisions, for "especially serious circumstances," maximum sentence up to seven years fixed-term imprisonment.
-
For other participants (such as rotation authors, secondary developers, sales agents, etc.), will be convicted and sentenced according to their position, role, and illegal profit amounts in this operating ring; sentences will be lighter than principals, possibly under three years or suspended sentence, similarly subject to fines and confiscation of illegal proceeds.
8. Predictions on Future Cheat Evolution Trends
The downfall of the "Sopabox-cn" ring, rather than a successful siege, was more like public execution of its own amateurishness. However, we must soberly recognize their failure will become future peers' "negative example." A more seasoned, more professional criminal organization will learn from their mistakes, evolving into harder-to-track and strike forms.
Based on analysis of "Sopabox-cn" ring's weaknesses, we can deduce how a more resilient advanced cheat ring would operate. Its core principles will revolve around: "absolute anonymity, technical barriers, de-risked business models, centralized community management, and contingency crisis handling."
8.1 Operational Security: Absolute Anonymization (OpSec)
"Sopabox-cn" ring's biggest failure was never truly separating virtual from real identities. Future criminal organizations will eliminate this from the root.
1. Identity Isolation and Anonymization:
- Primary principle is never using any information associated with the real world, like real-name websites, Taobao stores, or personal social/payment accounts. "Suspected Core Operator A's" real-name information leak is typical negative example.
- Fund flows will be thoroughly encrypted. All transactions will complete through privacy-focused cryptocurrencies (like Monero/XMR) processed through automated payment gateways. Funds will be "laundered" through mixers, severing tracking paths, whether receiving payments or distributing shares to "rotation authors."
- Communications and development environments will be completely isolated. External communications use end-to-end encrypted anonymous chat tools; development work occurs in dedicated offline virtual machines with untraceable physical hardware.
2. Server and Infrastructure Concealment:
- Infrastructure will be decentralized and censorship-resistant. Servers distributed across different VPS in countries lenient on "abuse reports," all anonymously purchased.
- Cheat clients won't directly connect to fixed IPs but obtain latest server addresses through dynamic domains or decentralized storage (IPFS), increasing blocking difficulty.
- Server backends absolutely won't record identifiable user data like game IDs, IP addresses. "Sopabox-cn's" recording user character IDs behavior was tantamount to preparing "court evidence" for enforcement departments.
8.2 Technical Architecture: Building High-Barrier "Black Boxes"
"Sopabox-cn's" atrocious code quality was key to its breach. Next-generation cheats will make reverse engineering torturous.
1. Client Self-Protection:
- Adopt multi-layer encryption and dynamic loading; core code downloads in blocks from servers only after verification, decrypting and executing in memory.
- Use top-tier virtual machine protection and code obfuscation (VMProtect/Themida), converting code logic into complex virtual machine instruction sets, greatly increasing static analysis difficulty.
- Built-in anti-debugging and anti-hook mechanisms; once analysis detected, program immediately self-destructs or provides false data.
- Might even adopt "polymorphic code" technology, making each user's client distributed with unique "code fingerprints," rendering signature-based detection methods ineffective.
2. Data "Deception" and "Temporality":
- Some core decision logic might execute on cloud servers; even if client reverse-engineered, can't obtain its "brain."
- Most importantly, preset "kill switch". Once major risk detected, operators can send commands from servers making all clients immediately stop working and self-destruct; servers themselves can one-click wipe. This proactive risk avoidance capability far surpasses "Sopabox-cn" ring's passive fleeing.
8.3 Business Model: Risk Isolation and Ecosystem Reconstruction
"Sopabox-cn's" model was too direct with concentrated risk. Smarter organizations would adopt "subcontracting" models isolating risk.
1. Layered Authorization, Risk Isolation:
- Framework developers retreat behind scenes, only responsible for developing and maintaining "unlocker core," packaging it as "advanced game development tool."
- They'll cultivate a "rotation author" ecosystem. Through high-barrier recruitment of top rotation authors, charging them hefty framework licensing fees, having these authors sell scripts to end users under their own names in private communities.
- This way, payments, after-sales, user disputes and other frontline risks all borne by dozens of "distributors" (rotation authors), while framework developers sit atop pyramid, far from direct conflict.
2. Pricing Strategy and Covert Marketing:
- Through high pricing filter out core high-value users (power-levelers, streamers, etc.).
- Marketing will be completely covert, only circulating in top player circles through "invitation" or "referral" systems, creating scarcity and premium atmosphere while further enhancing security.
8.4 Community Management: Centralization and Risk Control
User stupidity is the greatest risk source. Users like "Nobita" are walking bombs.
1. Absolute Centralization and Silence Rules:
- Users' first rule is "prohibit all forms of public discussion and showing off". Any users leaking information externally or generating disputes from cheat use will have authorization permanently revoked; their upstream "rotation authors" also subject to joint punishment.
- "Unstable elements will be quickly purged." Emotional users who attract trouble will be removed from authorization lists at first incident opportunity. Operators' goal is low-risk profit, not backing internet disputes.
- Won't leave survival space for "internal sources." Since operators' identities completely anonymous, income fully encrypted, and don't store user data. Even if investigators successfully penetrate, can't obtain key information locking real identities, eliminating "Sopabox-cn" ring's low-level mistake of total exposure from one Taobao store.
8.5 Conclusion: The Challenge of Confronting "Ghosts"
In summary, what we may face in the future will no longer be a "Sopabox-cn"-level makeshift operation full of holes, but criminal organizations in nearly "ghost" form. They have no physical presence, no traceable identities, high technical barriers, and extremely strong counter-reconnaissance and risk avoidance capabilities. When storms come, operators only need to press preset "kill switch" to evaporate from networks as if never existed.
This poses unprecedented challenges for game manufacturers, operators, and law enforcement, warning us that anti-cheat struggle will be a continuously escalating, never-ending technological and strategic game.
9. In-depth Analysis of "Sopabox-cn" User Profiles
At monetary cost, ignoring personal ability, energy, time, even game mechanics limitations, stably providing theoretically optimal game performance. Its user base isn't monolithic but an ecosystem of players pursuing different objectives.
9.1 Category One: Performance-Driven Players
This user type's core demand is data, efficiency, and results.
1. The Rank Chaser
- Profile: Like "Player D" in the report's incident origin, perfect embodiment. Such players are extremely obsessed with WCL (Warcraft Logs) scores and rankings. Their gaming enjoyment and social capital directly tied to "hitting purple, orange, even pink (95-100 score) logs."
- Core Pain Point: Manual operations inevitably have mistakes, and achieving extreme DPS relies not only on skill but "luck" factors like crits and trinket procs. They can't tolerate data imperfection caused by personal mistakes.
- Usage Scenario: During raids' farm phase when survival pressure isn't high, activate cheats to fully push personal data, obtaining impressive WCL battle reports for showing off in guilds, forums, or social media, or as "ticket" to join stronger teams.
- Psychological Motivation: Vanity, social recognition anxiety. They need external, quantifiable data to prove their value.
2. The Efficiency-Focused Booster
- Profile: Cheats' most loyal, highest-paying users. They make living from World of Warcraft, whether "M+ carries" or "raid boosting" (carrying bosses through Heroic/Mythic raids), time is money.
- Core Pain Point: Humans fatigue. Continuous 8-12 hour high-intensity boosting causes mental and operational decline, reducing efficiency, even "wiping" (failing). This directly impacts income.
- Usage Scenario: Full-time use during all "boosting orders." Cheats ensure each order completes most efficiently, stably. They can let cheats auto-output while handling customer communications, taking new orders, etc., achieving "one person multiple uses," maximizing profit.
- Psychological Motivation: Pure commercial interests. Cheats aren't toys but "productivity tools," fixed asset investments reducing costs and increasing output. 4800 RMB annual fee for power-levelers earning tens of thousands monthly is highly cost-effective investment.
3. The High-End Progression Raider
- Profile: Most covert, most controversial user group. They're in top guilds aiming for server first kills, even world first kills.
- Core Pain Points:
- Stability above all: During hundreds of progression attempts, any person's tiny mistake can cause wipes. They need absolutely stable, error-free output machines, freeing full focus for handling complex, rapidly changing boss mechanics.
- Avoiding "Plugin Taint": As technical analysis in report states, high-end players rely on complex WeakAuras and other addons for decision assistance. But at critical moments, these addons may fail due to "taint." While "Sopabox-cn" directly calls native functions, completely ignoring addon taint, providing "absolutely reliable" false assurance. This is deadly temptation for them.
- Usage Scenario: During high-intensity progression battles, especially in fixed-strategy "Raid-Helper tactical board" style encounters, using cheats to ensure personal rotation's "zero mistakes," becoming reliable "DPS target dummy" in the team.
- Psychological Motivation: Extreme utilitarianism and pursuit of "controllability." For team victory, willing to use any means improving success rate, viewing cheats as tools eliminating "human weaknesses" (like fatigue, panic).
9.2 Category Two: Experience-Driven Players
This user type doesn't necessarily pursue extreme data but hopes to overcome certain obstacles for smoother or easier gaming experience.
1. "Aging Veteran / Players with Disabilities"
- Profile: Older players whose reaction speed, APM, and sustained focus naturally decline with age. Another portion has hand injuries (like carpal tunnel) or other physical disabilities unable to complete complex keyboard operations.
- Core Pain Point: They love this game world, love adventuring with friends, but physical or energy limitations prevent them from dealing adequate damage, becoming "burdens" in friends' eyes, generating frustration and social isolation.
- Usage Scenario: When participating in routine raids or M+ with friends and guild members. They don't seek top data, just "not holding back," keeping pace with the group, enjoying social fun.
- Psychological Motivation: Maintaining social connections, overcoming physiological barriers, seeking belonging. For them, cheats are (illegal) "assistive technology," compensating for physiological deficiencies.
2. "The Burned-Out Player / The Alt-aholic"
- Profile: Players who've played for years, tired of constantly learning new versions, new classes' tedious rotations. Or those with many alts hoping to quickly gear them but unwilling to invest substantial energy practicing each character.
- Core Pain Point: High learning costs, tedious repetitive labor. They only want to experience game's core content (story, boss fights, gear collection), not spend time on "target dummy practice" or "practicing rotations."
- Usage Scenario: When playing alts or unfamiliar classes, directly activate cheats, skipping learning curve, enjoying "instant mastery." During daily questing, dungeon farming, letting cheats handle it while they watch shows, chat.
- Psychological Motivation: Pursuing convenience, escaping repetitive labor, paying for "ease." They have considerable spending power and willing to pay for saved time and energy.
9.3 Category Three: Special-Purpose Players
1. "The Script Researcher / The Rotation Author"
- Profile: This group may themselves be top players or deeply knowledgeable about game mechanics. They're part of "Sopabox-cn" ecosystem, namely the "over 20 rotation authors" mentioned in report.
- Core Pain Point/Demand: They're unsatisfied with using; they want to "create." They profit by writing and optimizing class rotation scripts running on "Sopabox-cn" platform. The cheat platform provides them a channel to "monetize" game understanding.
- Usage Scenario: Purchase cheat core, using its provided development environment to debug and test self-written scripts, selling them to other users.
- Psychological Motivation: Technical exploration, knowledge monetization, establishing "guru" reputation within niche circles.
9.4 Summary and Additional Notes on "Sopabox-cn" User Profiles
- Common Psychology: Regardless of category, all users display "outcome justice" tendency—i.e., to achieve certain goals (high WCL score, earning money, team victory, relaxed gaming), using cheats as "procedurally unjust" means is acceptable.
- Price Filtering: "Sopabox-cn's" high pricing itself is user filtering mechanism. It excludes true "newbies" and purely casual players, leaving behind core users with clear purposes, strong demands, and sufficient paying capacity. This makes its user base more "elite" and "professional" than generally imagined.
- Community and Culture: Report mentions this cheat has QQ groups with thousands of members, indicating formation of subculture community. Within this community, cheat use is rationalized, normalized, even generates hierarchy (e.g., whose rotation scripts are better, whose WCL scores higher). This closed community environment further reinforces users' mistaken cognition, making them feel "everyone's using it, nothing wrong with me using it."
In summary, "Sopabox-cn's" user spectrum is extremely broad, from WCL score chasers pursuing fame and fortune to professional power-levelers viewing it as production tool; from top progression raiders seeking stability to burned-out veterans just wanting relaxed gaming. They span technical level, gaming objectives, and spending capacity dimensions, jointly constituting a gray ecosystem attached to World of Warcraft, destroying game fairness and culture.
10. Technical Appendix: Classification of World of Warcraft Cheat Types
Many people can't accurately distinguish between "one-click macros" and "cheats" using "macro" name for confusion. Distinction method is simple: "In-game built-in functions are legitimate; anything requiring third-party software is a cheat."
But many self-media oversimplify cheats as "memory hacks," which isn't accurate. This "Sopabox-cn's" technical essence is Memory Reader/Unlocker, not more violent Memory-Write Cheat.
World of Warcraft cheats mainly divided into three types:
- Pixel Bot
- Unlocker
- Memory-Write Cheat
10.1 Pixel Bot
This is the oldest, most primitive, also most "dumb" cheat form. You can understand it as a tireless robot staring at your screen; it can only "see," cannot "understand."
What's its principle?
- Fixed Target Detection: Cheat developers pre-write a script. For example, setting: action bar 3rd slot, coordinates (123, 456), what color when skill is ready, what color on cooldown.
- Color Recognition: Cheat program like a camera fixated on those few pixels on screen. Once (123, 456) color changes from "CD gray" back to "highlighted," it determines: "skill available."
- Key Simulation: After determination, it calls system API, pretending your hand pressed '3' key on keyboard. Throughout this process, it knows nothing about what's really happening in-game.
Why say it's dumb?
- Extremely fragile: You change UI skin, adjust resolution, move action bar one slot—all its preset coordinates and colors invalidate, instantly broken.
- Low efficiency: High-frequency screenshot color comparison severely drags down CPU, making gameplay feel like watching PowerPoint.
- Information blind: It only knows "skill lit up," doesn't know "skill still 1.5 seconds from ready" or "target's DOT has 3 seconds left." This information deficiency makes it seem foolish in any scenario requiring complex judgment.
How to counter it?
Warden anti-cheat system disdains checking your screen colors, but your robot-like precision—pressing within 0.01 seconds after every cooldown ends, no delay variation—in its eyes is like fireflies in dark night, impossible not to notice.
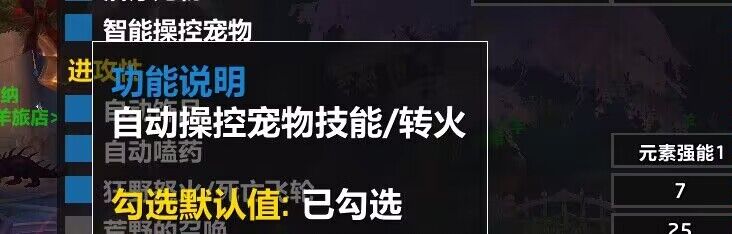
10.2 Unlocker
This is "Sopabox-cn's" true face. No longer a blind screen-watcher but directly invading game's brain—memory, reading everything about you, unlocking shackles Blizzard placed on you.
What's its principle?
- DLL Injection: All evil's beginning. Cheat injects its written malicious code (DLL file) virus-like forcibly into game process (
Wow.exe). From this moment, its code and game code under same roof, doing whatever it wants. - Pointer Scanning: This is reverse engineering work. Each game startup, your HP bar's memory address changes. But cheat developers through analyzing game files can find a fixed "landmark" (base address), then holding a "treasure map" (offsets), winding around always precisely reaching your HP, MP, skill CDs, buff remaining times—accurate to decimal places.
- API Unlocking: This is the core. Blizzard built a "sandbox" for ordinary plugins (Addons), strictly limiting their capabilities. In combat, want plugins to help you cast unconditionally? No way. This is Blizzard's red line. And unlockers, using their injected code, directly cross this red line, finding game engine's internal native C++ function actually used for casting spells, then—directly calling it.
What can it achieve?
It lets a purchased script, in the cheat's built-in Lua engine, read with zero delay target HP percentage, own resource values, all skill precise cooldown times, all Debuffs on target's remaining ticks and duration ......Then, based on this perfect information, at reaction speed surpassing human physiological limits, making optimal decisions for you, calling "unlocked" functions, pressing skills for you.
Essentially, a cold, emotionless, absolutely rational output machine wearing your character's skin. Anomalous data on WCL rankings comes from this.
Ignoring "Addon Taint"
This is its most insidious, most tempting selling point to high-end players.
- Let me explain what "addon taint" is. Blizzard designed a "security check system" to prevent addon-automated combat. When your addon (like extremely complex WeakAuras) executes operations considered "unsafe" (like checking other players' talents in combat), entire code execution environment gets "tainted." Once tainted, any subsequent attempts to call protected combat functions (like using skills, items) get directly blocked by system with annoying error: "Interface action has been blocked by addon."
- For players pursuing extremes in raids, this is nightmare. At critical moments, a carefully designed macro or addon function suddenly fails, possibly directly causing wipes.
- So, what's "Sopabox-cn's" solution? "Simple and brutal: doesn't go through this security checkpoint at all."
- Addon taint is Blizzard's rule inside Lua sandbox environment. While "Sopabox-cn" through DLL injection, its core code runs outside sandbox, directly dialoguing with game's C++ underlying engine. It calls casting functions, taking a VIP channel without "security checks." Therefore, no matter how severely your game interface is "tainted" by ordinary addons, its automated rotation is completely unaffected.
- It not only auto-plays rotations but solves "addon taint" problem that vexes even top players, creating false impression of "more stable operation, smoother gameplay." This is precisely the poison that can deceive and attract core players who should resist cheats.
How to counter it?
DLL injection, memory scanning, hooking game functions—these behaviors themselves are self-reporting to Warden system. I handed out "Sopabox-cn's" client code samples, equivalent to packaging these rats' genetic maps and detailed addresses together and delivering to the cat. Blizzard can extract from it hundreds of thousands of unique "code fingerprints"; thereafter Warden scanning any player's memory, once matching fingerprints discovered, can directly ban, catching every one.
10.3 Memory-Write
This is most brazen, also dies fastest. Unsatisfied with "reading," it wants to directly "write," attempting to change game rules.
What's its principle?
Like unlockers, first inject, then scan addresses. But final step isn't calling functions but directly modifying memory values. For example, changing memory value representing your movement speed from 1.0 (100%) to forcibly 8.0 (800%), achieving teleportation; or directly modifying your coordinate X, Y, Z values, letting you walk through walls and underground.
Why can't it survive in WoW?
Because Blizzard isn't stupid. Modern online games' core data all adopt server-side authoritative verification. Your character's HP, position, money—server has a copy as final arbiter.
You use cheats on your computer to make yourself a god; this data synchronizes to server, server's "ledger" cross-checks: "You're not right." Next second, you either get forcibly pulled back to origin by server's "might," or directly receive ban notice, kicked from game. Such cheats typically only can dominate in some weakly protected private servers or ancient standalone games.
10.4 Summary Table of Three Cheat Types
| Characteristics | Pixel Bot | Memory Reader/Unlocker | Memory-Write |
|---|---|---|---|
| Core Principle | Screen color recognition, input simulation | DLL injection, memory reading, unlocking and calling native functions | DLL injection, directly modifying memory data |
| WoW Representatives | Fishing bots, simple grinding scripts | "Sopabox-cn", Honorbuddy (HB) | Teleporting, wall-hacking (virtually nonexistent on official servers) |
| Invasiveness | Low (external process) | High (injecting into game process) | Extremely high (injecting and modifying memory) |
| Precision/Capability | Low, vague information, limited functionality | Extremely high, obtaining all data, executing complex logic | Changes game rules but easily detected by server |
| Fragility | Extremely high (sensitive to UI, resolution) | Medium (sensitive to game version updates) | Extremely low (just need to find address to modify) |
| Detection Difficulty | Relatively difficult (requires behavioral analysis) | Relatively easy (Warden's primary strike target) | Easiest (server-side authoritative verification) |
10.5 Rotation Authors vs. Unlocker Core Authors: The Gap in Roles and Technology
- Unlocker/Cheat Core Authors: They are "infrastructure engineers" and "hackers". Their work occurs at underlying level of World of Warcraft "building."
- Core Technologies: C/C++, assembly, reverse engineering, memory reading/writing, DLL injection, hooking technology.
- Work Content:
- "Breaking Walls": Bypassing or disabling Blizzard's Warden anti-cheat system, first step and most critical step.
- "Building Bridges": Through DLL injection, forcibly inserting their code (unlocker core) into game's process (
Wow.exe), making their program fuse with game. - "Laying Pipelines": In game's vast memory data ocean, through reverse analysis, precisely locating all key information's memory addresses.
- "Opening Backdoors": This is "unlocker's" core. Finding game engine's internal C++ native functions, exposing these "protected" functions, turning them into "backdoor APIs" callable by rotation authors.
- "Building Platform": Building a lightweight Lua script execution environment. This environment is rotation authors' stage.
- Rotation Authors: Are "tactical designers" and "game understanding 'translators'". Rotation authors' work occurs on Lua platform built by cheat authors; rotation authors are this "building's" "interior designers".
- Core Technologies: Deep game understanding, Lua scripting, data analysis (WCL, SimC), logic construction.
- Work Content:
- "Translate" Tactics: Rotation authors translate optimal output methods researched by community into precise, rigorous computer logic code.
- "Write" Brain: Rotation authors using "super API" provided by cheat authors, write extremely complex decision trees (or state machines) in Lua.
- "Optimize" Details: This truly shows a rotation author's skill level
In summary, rotation authors don't touch game's underlying, don't do reverse engineering. Rotation authors create upper-level logic within "rules" provided by cheat authors. Unlocker authors provide weapons; rotation authors write instruction manuals and auto-aim programs.
10.6 Skill Tree Analysis of "Rotation Authors"
Skill Tree 1: Top-tier Class Understanding—Far More Than "Playing Well"
- You must be this class's "mathematician." "Playing well" is just foundation. You need to completely deconstruct a class's output model into mathematical formulas.
- WCL is your textbook. You must analyze WCL data of world's top players, not looking at how high they parsed but why they made certain decisions at certain timestamps.
- Familiar with all combat scenarios. Single-target, two-target, three-target cleave, mass ADD (trash) handling—your script must prepare contingencies for all situations.
Skill Tree 2: Mastering Lua Programming—Dancing Within Cheat Framework
- Familiar with Framework API: Getting an unlocker, first thing is studying its documentation (if any), or testing all functions it provides yourself.
- Code Optimization: Your script may run dozens even hundreds of times per second. Any redundant calculations, inefficient loops will increase CPU burden.
- Logic Robustness: If a function returns
nil(null value) in some situation, will your entire script crash?
Skill Tree 3: Real Combat Complexity—Vast Difference Between Melee and Ranged
- Melee "Simplicity": Melee class logic relatively clear, like a math problem.
- Instant Feedback: Most skills are instant cast, press and get result.
- Fewer Variables: Don't need to consider projectile travel, almost no casting.
- Ranged "Inferno": Ranged class implementation is gambling in chaos.
- Cast Time: Biggest difficulty. During your Fireball's 1.5-second cast, target might die or move behind pillar.
- Latency: Your computer (client) shows skill cast, but due to network latency, server might not have received it.
- Travel Time: Like Chaos Bolt, Blizzard—spells with flight time, problem more severe.
- Buff/Debuff Management (Snapshotting & Pandemic): Many damage-over-time (DoT) skills' damage depends on your stats the moment you cast them.
- Server Tick: Game servers don't process information continuously but settle DoT damage, mana regen, etc. at fixed intervals (Ticks).
Cheat authors provide firearms and ammunition. Rotation authors, through deep deconstruction of game mechanics and code implementation, install "red dot sight, laser pointer, custom trigger, and smart fire control system" on this gun, selling finished products to those who only need to pull triggers.
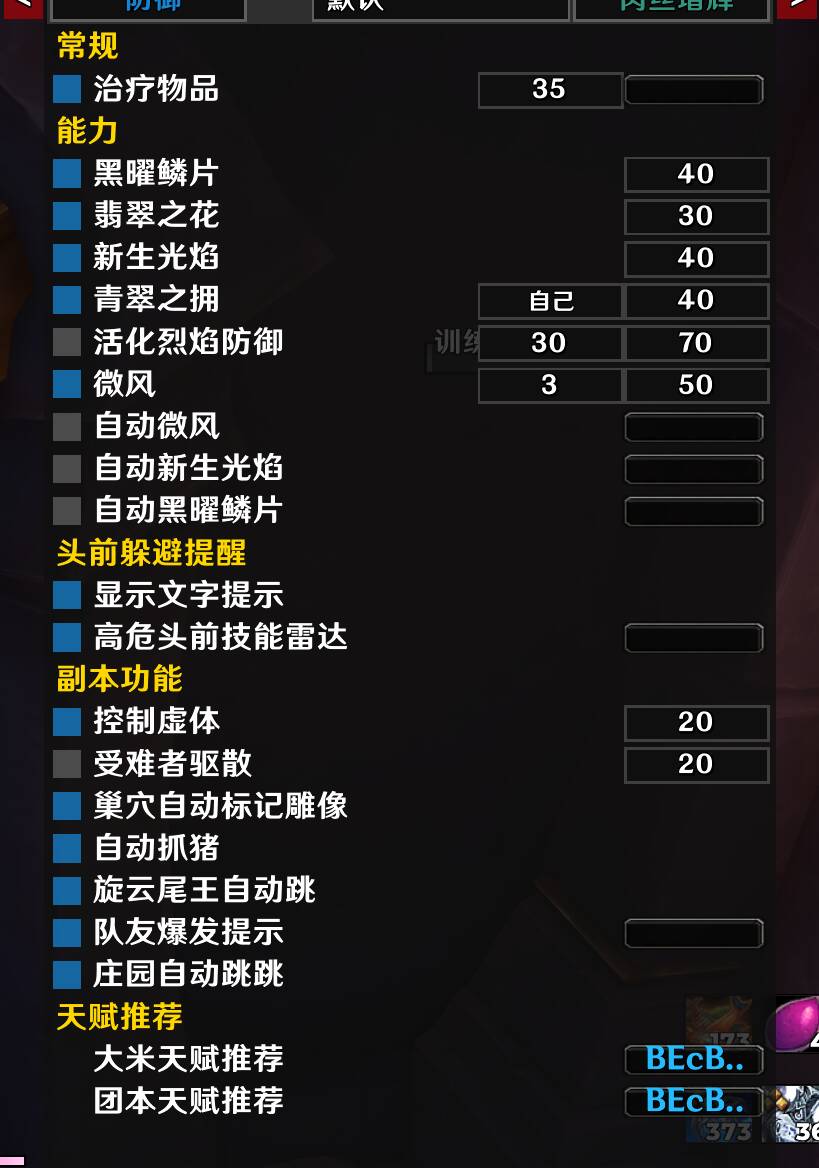
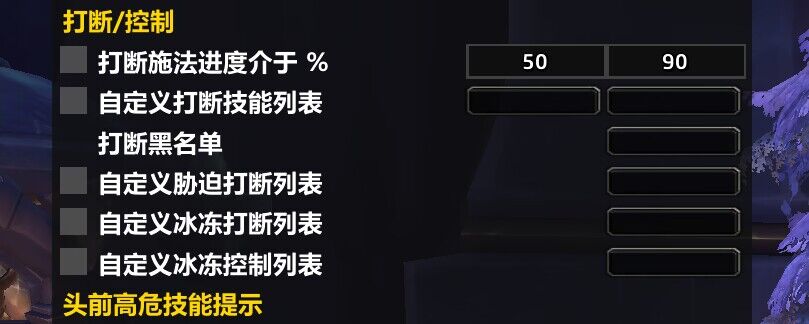
10.7 Technical Analysis Report (Sopabox-cn/GES)
This section provides in-depth technical analysis of "Sopabox-cn/GES" (i.e., "Sopabox-cn's" new name) cheat, aiming to reveal its working principles, security mechanisms, and interaction methods with game process. Analysis used IDA Pro 8.3 for static analysis, x64dbg for dynamic debugging, core target being GSE.exe.
1. Server Communication and Verification Mechanism
- Startup and Login: When GSE.exe starts or users log in, program first requests
http://retail.zhucedun.cn:999/for card key verification. - Backend Server:
http://retail.zhucedun.cn:999/is GSE's backend server, responsible for verifying whether user-purchased card keys are valid. - Data Transmission: After successful verification, user validity data (including authorization info, available rotation lists, etc.) passes through shared memory (using
CreateFileMappingfunction, Key is_communication_data_rtl_) to local GSE client. - Data Sample (JSON format):
{ "action": "callPHP", "clientid": "9199DE6C-DBC6-40f3-AA84-5FB4B4C82DDB", "fun": "getAllPersonalRotation", "m1": "d86b1aa0dbaf6795586c35e8d7469120", "m2": "72d29554986c112df3563f0ecc47e45f", "m3": "b34b136e065fd042f525b103c378ed6f", "mcode": "cec94b5b-5240-0eca-faa3-588c37ac7f2e", "para": "%5B%22ffffff%22%2C%22ad64003c43b1935108c35e6962643e21%22%5D+", "sid": "815b4e87-be01-4fcf-97db-cd61a946fa00", "t": "1722127804", "user": "ffffff", "uuid": "F6A0C2CF-0CDE-4a21-9E6C-961BEE595934", "webkey": "4d9acb802f2b89797e7af16945208ecc" }
2. Anti-Cracking and Code Injection Mechanism
- Anti-Cracking Verification: GSE client deployed multi-layer code countermeasures before executing core functions.
- Process Monitoring and Privilege Escalation: GSE client actively monitors
wow.exegame process. Once detectingwow.exerunning, program usesOpenProcessfunction requesting high access privileges. - Memory Allocation and Permission Modification: Through
VirtualAllocExfunction allocating a region inwow.exeprocess's memory space. Subsequently, usingVirtualProtectExfunction modifying that memory region's permissions. - DLL Injection and Reflective Loading: Using
WriteProcessMemoryfunction, writing program's embedded DLL file into memory space allocated inwow.exeprocess. ThroughCreateRemoteThreadfunction, creating a remote thread inwow.exeprocess pointing to injected DLL's loader (ReflectiveLoader).
3. Core Working Code and Lua Framework
- Core Function Code: Injected DLL code primarily implements cheat's core functions. Analysis shows C++ portion implemented some key underlying functions, like function named
xliGkRoBDo, containing 27 functions involving file operations, unit/object-related operations, game logic interaction, data reporting, security and verification. - Lua Framework: GSE client embeds a Lua interpreter. "Rotation authors'" written scripts run in this Lua environment. C++ portion provides API collections calling underlying game interfaces, while Lua scripts utilize these APIs to implement complex game logic.
4. Data Processing and Communication Samples
- HTTP POST Request Parameter Sample:
&sid=815b4e87-be01-4fcf-97db-cd61a946fa00&uuid=1424B166-C414-4e3a-B82A-5B1936E0E424&t=1722186190
5. Technical Summary
- GSE cheat's core technology is DLL injection and reflective loading, obtaining game data through memory reading, utilizing unlocked functions to bypass game's native security restrictions.
- It provides a Lua script runtime environment allowing "rotation authors" to write customized class rotation scripts, achieving highly automated game operations.
- Its anti-cracking mechanisms include client code obfuscation and protection, plus reflective loading of its own DLL, increasing reverse engineering and detection difficulty.
Notably, GSE client's newly added WeChat scanning and local disk scanning functions suggest it may be collecting user privacy information, further increasing its potential legal risks and threats to users.
11. Other Discovered Cheats
Unlockers
According to investigation, while exploring the cheat ecosystem during "Sopabox-cn" investigation, discovered numerous "unlocker" software complementary or providing similar services. These software typically provide underlying game interaction capabilities for bots or automation tools, allowing subsequent scripts or rotations to function normally. All following platforms, I have fully investigated and reported to Blizzard; everyone better behave.
Windows Platform Unlockers
- Wrobot – Well-known Windows platform bot with multiple built-in automation functions
- Sin-bot – Windows platform unlocker with official combat routines and gathering functions
- Owl Bots – Windows unlocker supporting official combat routines
- GMR – Unlocker designed for Windows
- Nilname – Windows unlocker with official combat routine functions
- Project Sylvanas – Invitation-only Windows unlocker with official combat routines
- Daemonic – Windows unlocker not including combat routine functions
macOS Platform Unlockers
- Tinkr – Unlocker designed specifically for Mac operating system. After "Sopabox-cn" fell, many rotation authors and domestic cheat users turned to this platform; I suggest you surrender—we've mastered all your criminal evidence.
Invitation-Only Domestic Internal Unlocker Cheats
- TTOC
- HWT
- RD
- FR
Note: These tools typically optimized for specific game versions or private servers, obtainable only through invitation, with strong concealment and community nature.
Combat Routines
Combat routines are crucial in automated gaming processes, responsible for automatically releasing most effective skill combinations based on player character's class, talents, and current game state.
Multi-Unlocker Supported PVE Rotation Collections
- Phoenix Gaming – Integrated PVE rotation collection supporting multiple unlockers
- Caffeine – Powerful PVE rotation collection supporting multiple unlockers
- Baneto – PVE rotation collection compatible with multiple unlockers
- BadRotations – PVE rotation collection supporting multiple unlockers
- Murlocs – Widely used PVE rotation collection supporting multiple unlockers
- RaidRush Mists of Pandaria – PVE rotation collection focusing on MoP classic servers
Specific Class Rotations
- Dummy Series: Outlaw – Rotation script specifically for "Outlaw Rogue" class. Discord:
https://discord.gg/JN5W9nQaT5 - Dummy Series: BeastMaster – Rotation script for "BeastMaster Hunter" class. Discord:
https://discord.gg/JN5W9nQaT5
PVP Rotation Collections
- SadRotations Combat Routines – Rotation collection mainly targeting PVP scenarios. Discord:
https://discord.com/invite/A9Ca8mQJZs
Rotation Script Marketplace
- Aurora-wow – Online marketplace focusing on rotation script transactions
Pixel Bots / Macros
These typically are tools using screen pixel recognition and mouse/keyboard simulation to achieve automated operations, especially common in China's cheat market.
Foreign Well-Known Pixel Bots
- GGL – GGloader – Powerful foreign automation tool
- Rice Rotations – Foreign service focusing on in-game combat rotations
- MaxDPS Assistant – Assistant tool aiming to help players maximize output
- RotationLab – Service providing professional game rotation solutions
Domestic Pixel Bots
Retail Service:
- Leiji Yijian Hong (Thunder Chicken One-Click Macro) – Uses cloud server:
https://www.fxas.cn/ - Jiajia Yijian Hong (Jiajia One-Click Macro)
- Zhuzhu Xinshijie (Piggy New World)
- Xiaoyi Yijian Hong (Little Easy One-Click Macro)
- Guangming Jingxiu Yijian Hong (Bright Refined One-Click Macro)
- Laoli Yijian Hong (Old Lee One-Click Macro)
- Dali Yijian Hong (Big Power One-Click Macro)
- Baxin Yijian Hong (Bullseye One-Click Macro)
- Mangguo Yijian Hong (Mango One-Click Macro)
- Wukong Yijian Hong (Wukong One-Click Macro)
- Shougeizhe Yijian Hong (Reaper One-Click Macro)
Classic Servers:
- Baxin Yijian Hong (Bullseye One-Click Macro)
12. Related Links
- Original Soapbox Rotations Official Website:
http://www.soapboxrotations.com/(defunct; can query historical mirrors via Wayback Machine below) - Original Soapbox Rotations Official Twitter: https://x.com/soapboxofficial
- Original Soapbox Rotations YouTube Channel: https://www.youtube.com/@soapboxrotations
- "Sopabox-cn" Predecessor "Chinese Version Soapbox" Official Website:
http://www.wowsbr.com/(Registration Number: Yue ICP Bei 16057588-2) - "Chinese Version Soapbox" Early Taobao Sales Store: https://shop69527830.world.taobao.com/
- "Suspected Core Operator A" Associated Company "Dingtian Technology Co., Ltd." Info (Tianyancha): https://www.tianyancha.com/brand/b5190341125
- "Suspected Core Operator A" Associated Company Information (Tianyancha):
- "Sopabox-cn" Later-Period Card Merchant Platforms:
http://9527faka.com/(Please note access risks)https://www.cs3000.xyz/(Please note access risks)
- Wayback Machine (Internet Archive): https://web.archive.org/ (Key evidence source for this article)
- Warcraft Logs (WCL): https://www.warcraftlogs.com/ (Origin site of this incident)
13. Appendix: Related Evidence Screenshots
Investigation Origin (Post Deleted by NGA; Once Again Calling Out NGA Moderation)
Information Obtained from Wayback Machine

Critical Registration Information

Tianyancha Related Screenshots (Some Entities May Be Same-Name Coincidences)






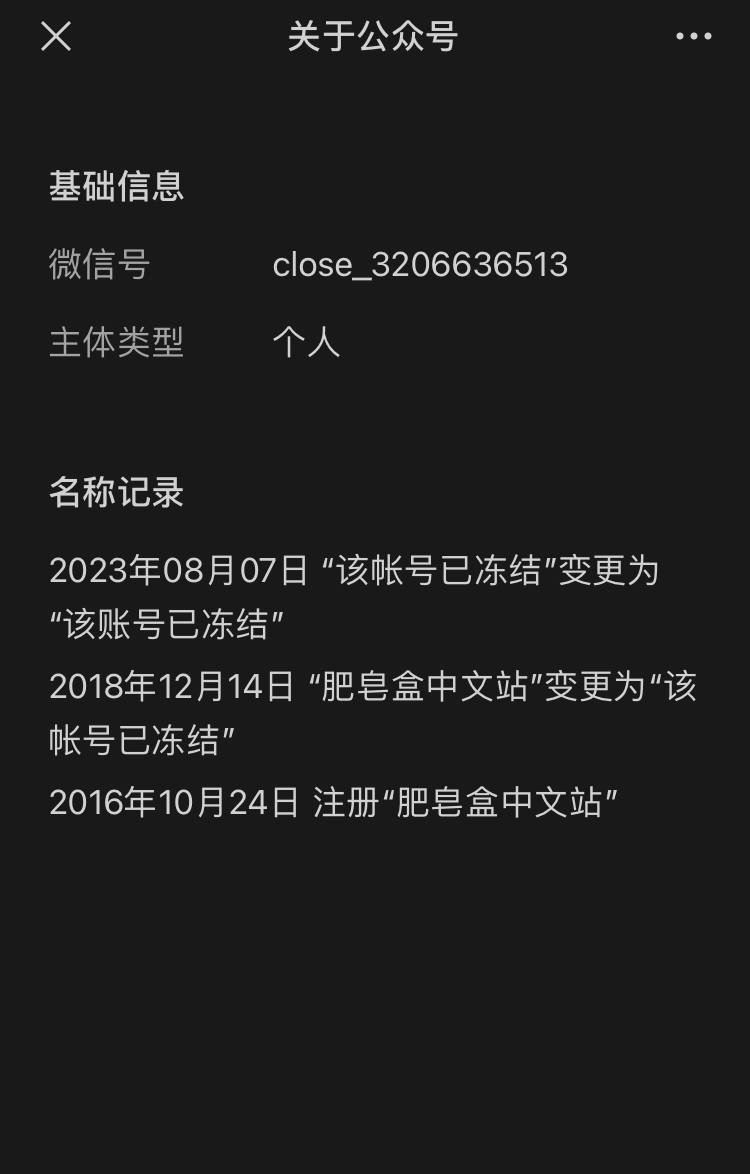
They Previously Had an Official WeChat Account
QQ Groups Can Estimate User Numbers (Now Disbanded)
Transfer Screenshots Provided by Internal Sources

Screenshots Provided by Hunter Who Reported to Me in 2024